A massive hack affected Twitter around 3pm EDT Wednesday (July 15th 2020), in which many high-profile accounts were used to tweet out a large-scale doubling scam.
It is unclear exactly how the hackers gained access to make the tweets from these accounts, but Twitter posted an update which corroborated reports that indicated company personnel and internal admin tools were involved.
Considering that the hackers had control over some of the most influential accounts on Twitter, posting a simple Bitcoin scam and exposing their access is a curious choice. As Kris Holt said, It could have been a lot worse - Accounts were frozen quickly, and the main known hacker address only received around $120,000 worth of BTC at the time of writing. Tracking these funds, however small the amount, is important and the FBI is reportedly investigating:
Tracking Funds
Bitcoin is a public blockchain, so anyone can pull and investigate all of the hack-associated transactions and addresses from their own node. Zach Finzi and I use this publicly available blockchain data to model the funds received and subsequently sent by the scammer(s).
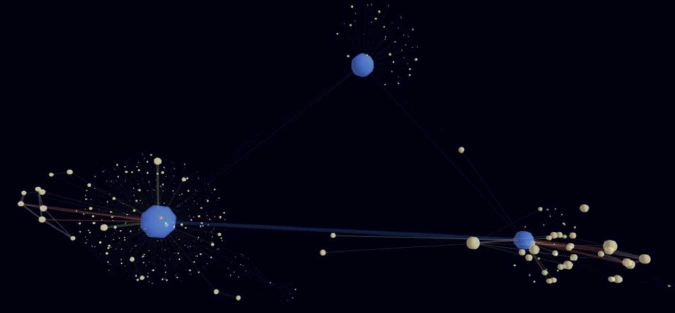
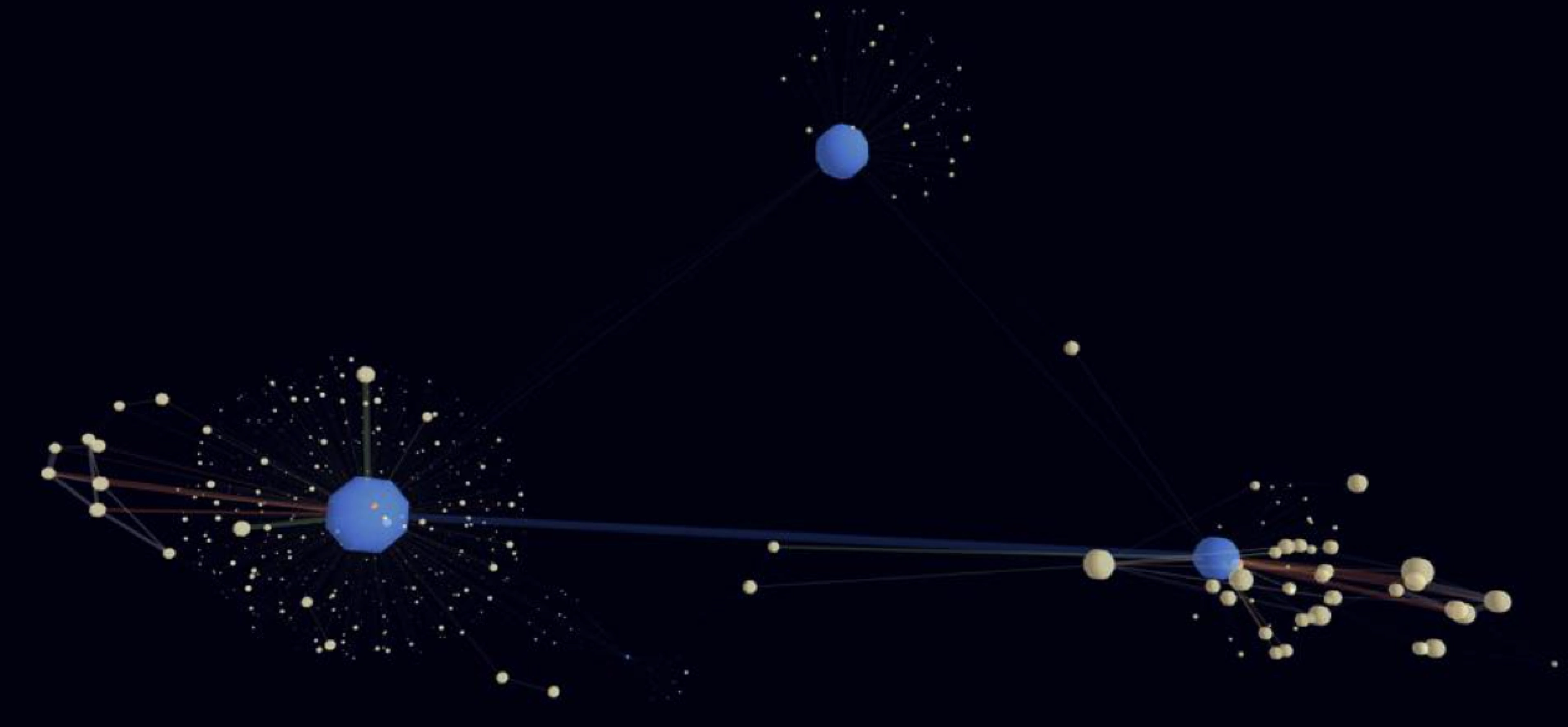
The above graph uses the 3d Network Topology App for Splunk SPLK +5.1%’s Machine Learning Tool Kit. It shows the indexed transactions between addresses implicated in the scam. Each node represents an individual address and the edges represent a set of transactions and transfers of BTC between the two nodes. Blue nodes are those linked to the Twitter hack, and blue edges represent transactions between them. Green edges represent funds received by the hacker(s), and orange ones show where they sent their funds.
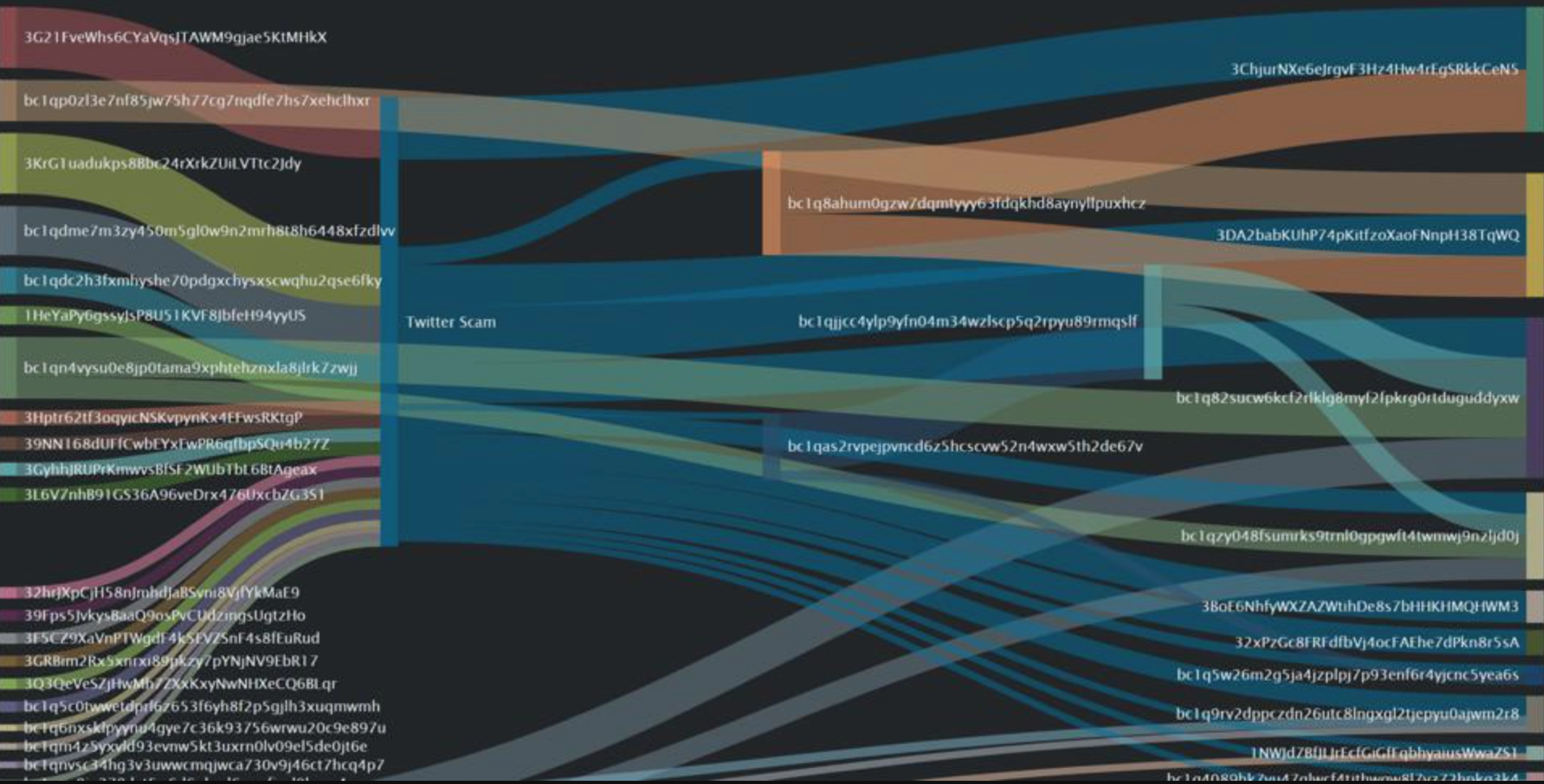
To better visualize the movement of funds we can use a Sankey diagram:
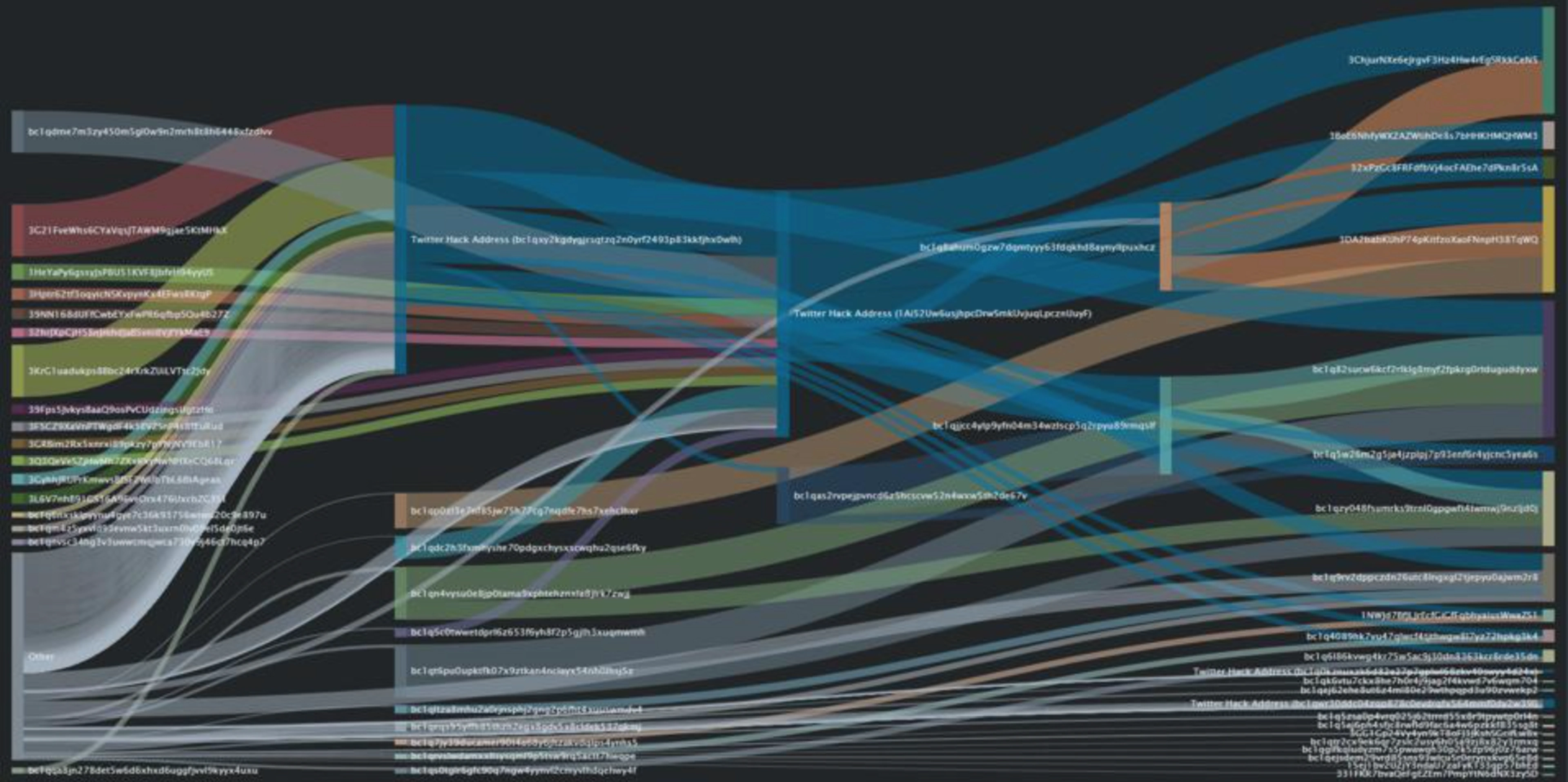
In the above image, transaction directionality can better be seen (BTC moves from addresses on the left to those on the right). To reduce complexity, not all transactions or addresses are pictured.
The primary address which the scammer collected payments with, and was linked on the “cryptoforhealth” website, before it was pulled down, can be tracked by anyone here.
The addresses which now hold these funds can further be monitored in an attempt to see if they eventually are transferred to a known entity such as a regulated cryptocurrency exchange or gambling service, and to prevent the spending or laundering of them.
Natural Language Processing of Bitcoin Scam/Hack Events
Due to the high-profile nature of the accounts hit, the large security concerns that come with such an attack are perhaps more important than the missing $120k.
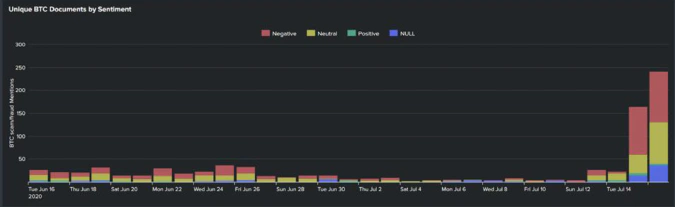
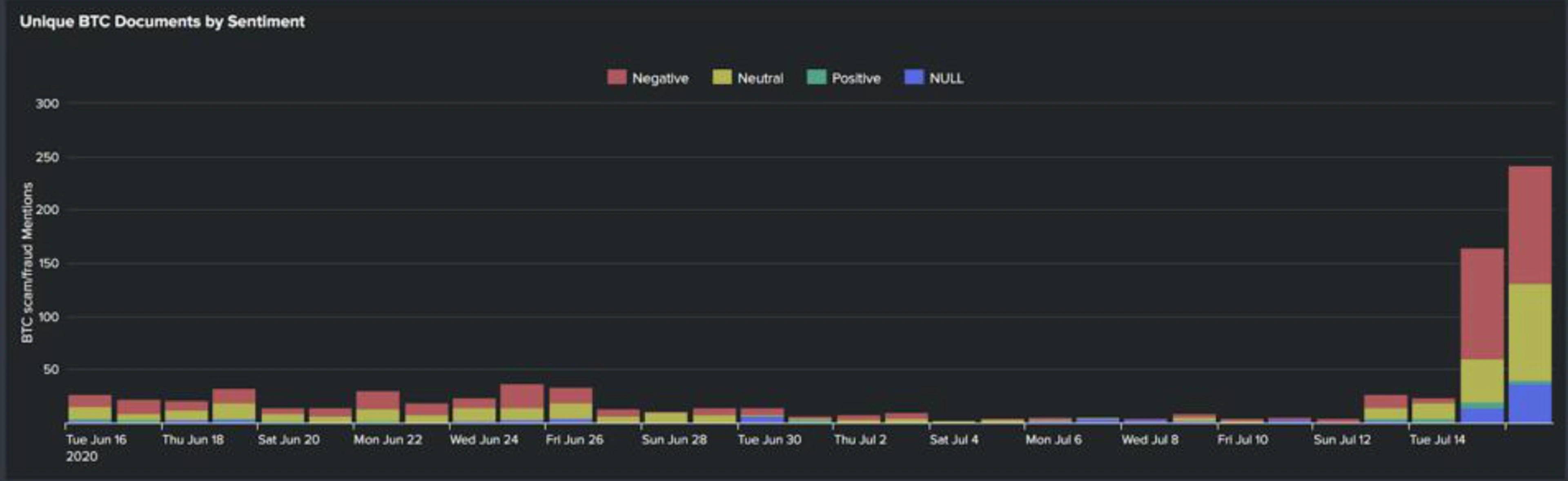
By combining techniques such as keyword detection, topic modeling, sentiment analysis, and named-entity recognition, I analyze natural language data surrounding Bitcoin. The below graphs shows unique document URLs (which are equivalent to unique articles, but also can contain structured text derived from images or videos) which contain the key term Bitcoin (and its aliases, such as BTC) and have topics related to scam, fraud, or hack.
The first image shows a daily count of the number of documents with the above criteria sorted by average term sentiment (that is sentiment in relation to the term “Bitcoin”). Expectedly, we can see a massive spike on July 15th and 16th.
By taking these filtered Bitcoin mentions, and limiting to only events from July 15th and 16th, we can see a highly negative average term sentiment (23.844%, where 0 is highly negative and 100 is highly positive). We also see that our models detect many mentions in these events for the high profile individuals whose accounts were compromised in this Hack:
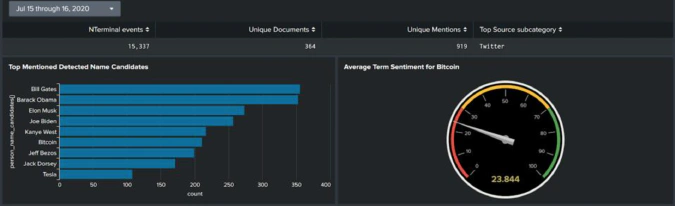
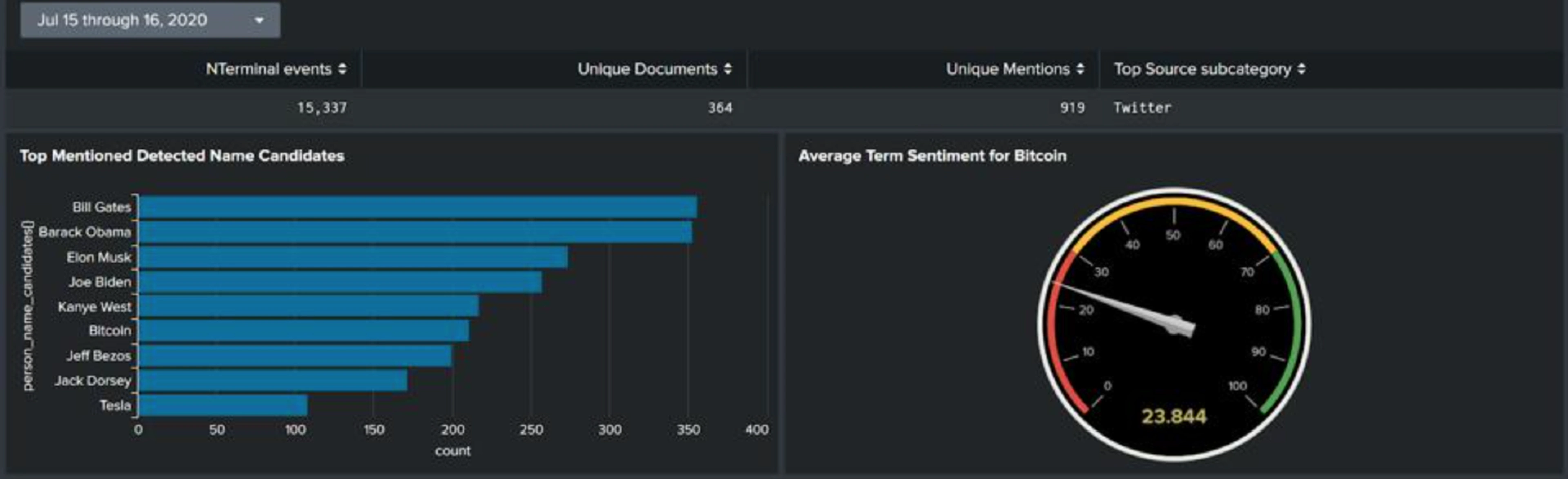
In the image above: Metadata about the information used in below panels (top). Top mentioned person name candidates identified through our neural nets (left). The overall sentiment for the term Bitcoin (right).
Despite the negative attention directed at Bitcoin, the incident does not imply any underlying security concerns for the Bitcoin network itself. In fact, the cryptofinancial ecosystem’s response to the hack has included spreading awareness of the scam, cooperative investigating of the activity, and reporting of the implicated addresses.
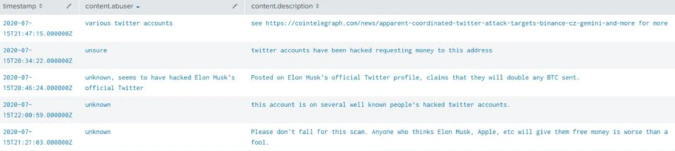
Bitcoinabuse.com, a site for self reporting of fraud-associated addresses, quickly received a number of reports for the scam addresses: