Having a powerful analytical tool that can provide an ample market overview might be very helpful, especially when attempting to understand the bigger picture in the market. To understand the crypto market, one has to understand its problems. Hacks and data breaches, that even institutional players appear to be vulnerable to, are a common problem. Most of the current approaches to investigating the breach focus on tracking the stolen funds by means of blockchain forensics tools. However powerful and helpful these tools may be, it is often not enough to recover stolen funds.
This investigation aims to collect disparate data sets and analyze it via Inca Digital on Splunk. Instead of looking at one type of data, Inca Digital applies a multifaceted approach to analysis and aggregates blockchain, financial, and natural language data, which provides a more complete picture of the market at the time the following events took place. It helps examine the problem from different angles, scrutinize and uncover the patterns that hackers use, and creates a basis for further analytical implications.
On August 2, 2016, the popular cryptocurrency exchange Bitfinex was hacked. Nearly 120,000 BTC were stolen from customers’ accounts, which equals to over $1 billion nowadays based on the current rates. As soon as the breach was discovered, all the withdrawals and trading were halted. Immediately after the breach, the price of bitcoin dropped 20%.
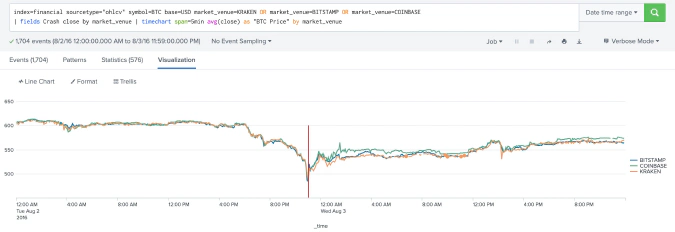

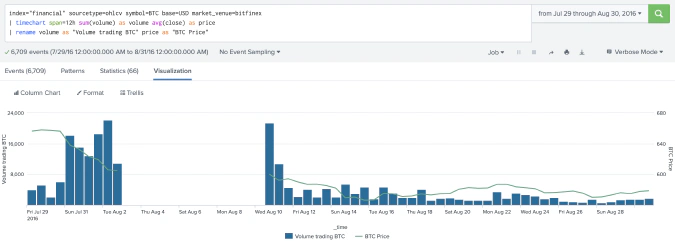
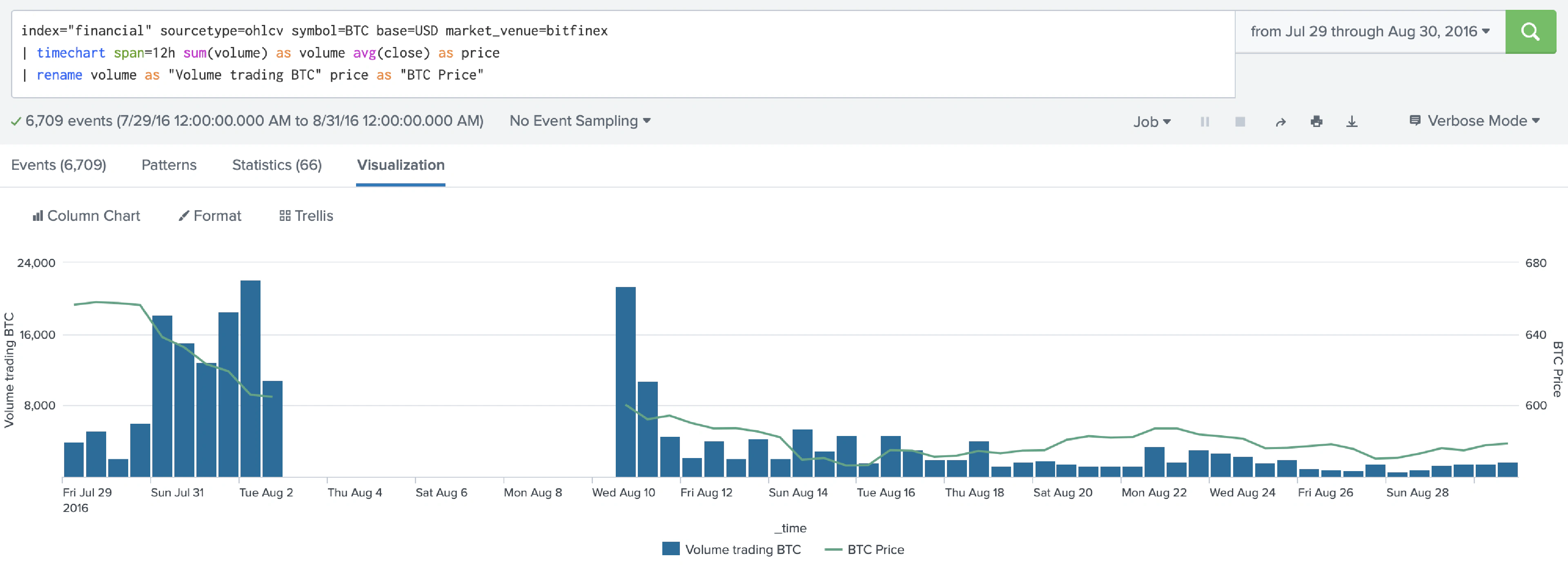
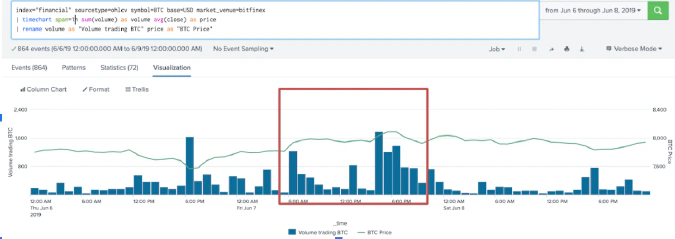
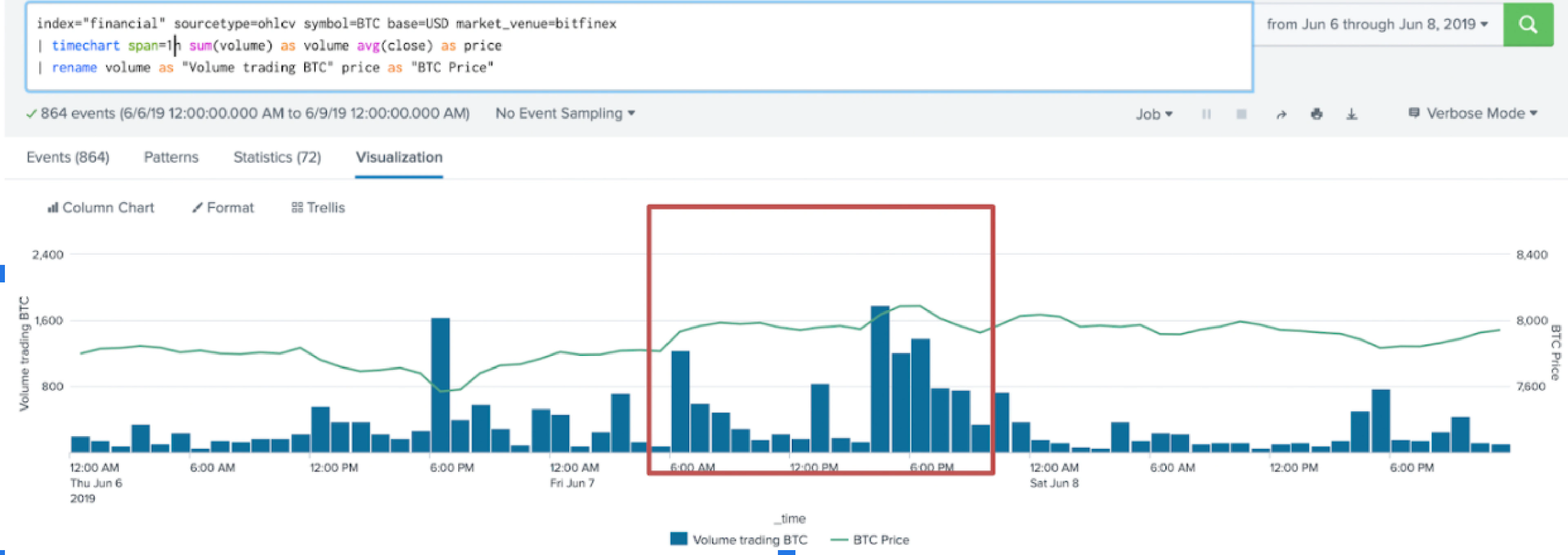
Up until June 7, 2019, when hackers first moved around 185 BTC to an unknown address, the stolen funds remained untouched. Having done it several times, hackers revealed their spending pattern, which shows that they move their digital assets accordingly with the BTC price fluctuations. The moves of the coins can also be easily observed in regard with the increase in trading volumes amid steady price growth.
Despite the fact that there is a significant number of investigations, which intend to track the stolen funds and detect those responsible for the hack, little is known about the hackers or the possibility of retrieving the funds. Since 2016, the only visible progress made is the return of approximately 27.7 BTC to Bitfinex by the US government, which represents only 0.023% of the total stolen assets.
The lack of reliable data leads to different kinds of speculation in the media. For example, in summer 2019, two Israeli crypto–enthusiasts were caught by the cyber unit of the Israeli Police. That time the alleged connection of two Israelis to Bitfinex Hack was actively pushed through the media. The involvement of hackers in the multi-million dollar hacking of Bitfinex seems exaggerated in the media due to the absence of other theft suspects and the lack of details from the police. As the classic phishing scam is said to be the brothers’ main method of committing their cybercrime, their participation in the original Bitfinex Hack is highly doubtful.
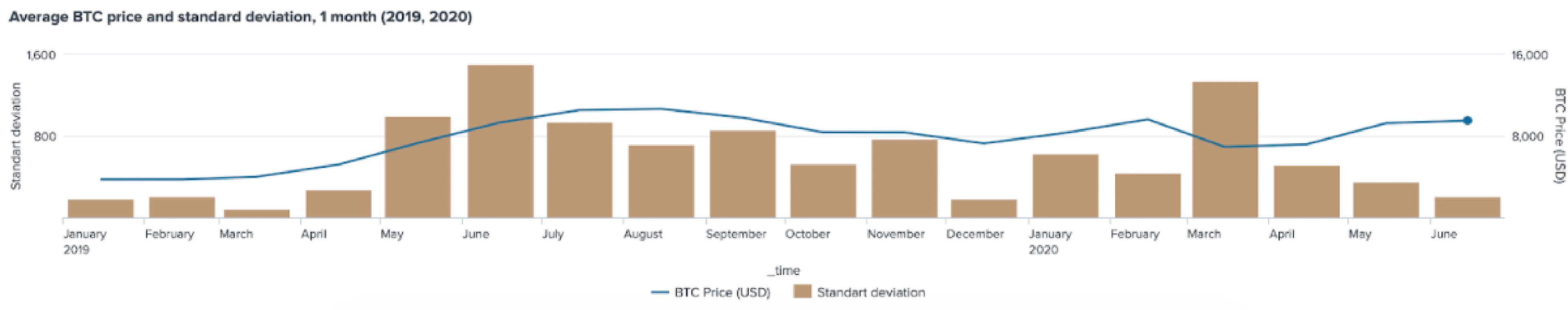
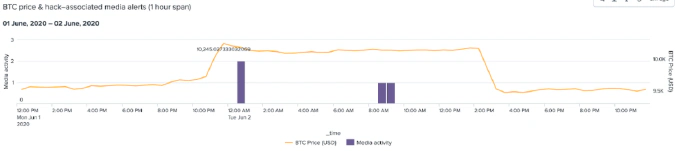
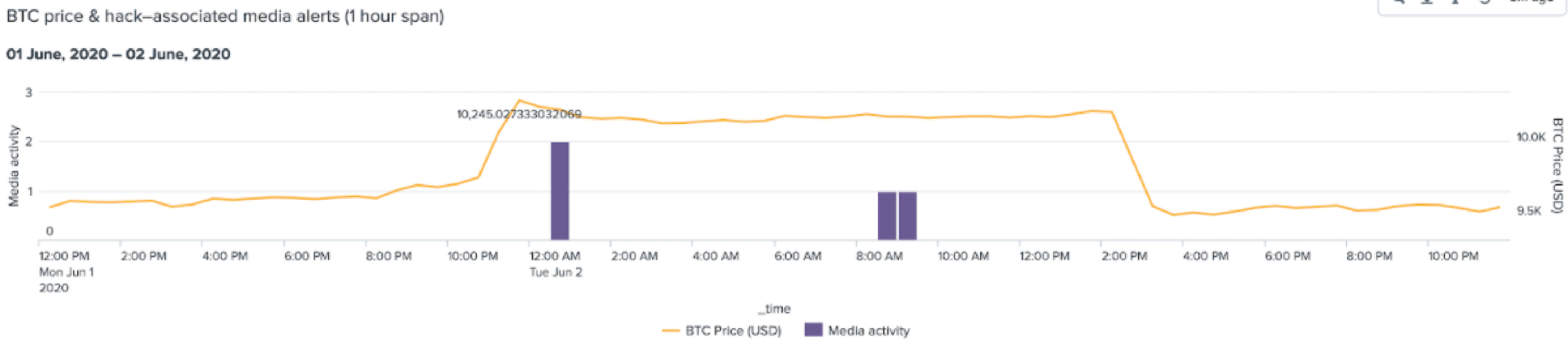
The general rush around the news about the movement of money is accompanied by a sharp increase in the negative perception of Bitfinex. This becomes obvious based on the sentiment analysis of the news that wrote about the hacking of the exchange in the days of the stolen funds movements. This distrust in Bitfinex is also observed from the corresponding BTC price fluctuations. Despite the relative flat price line on corresponding dates of stolen coins movement, the standard deviation bars show abnormal BTC price variation.
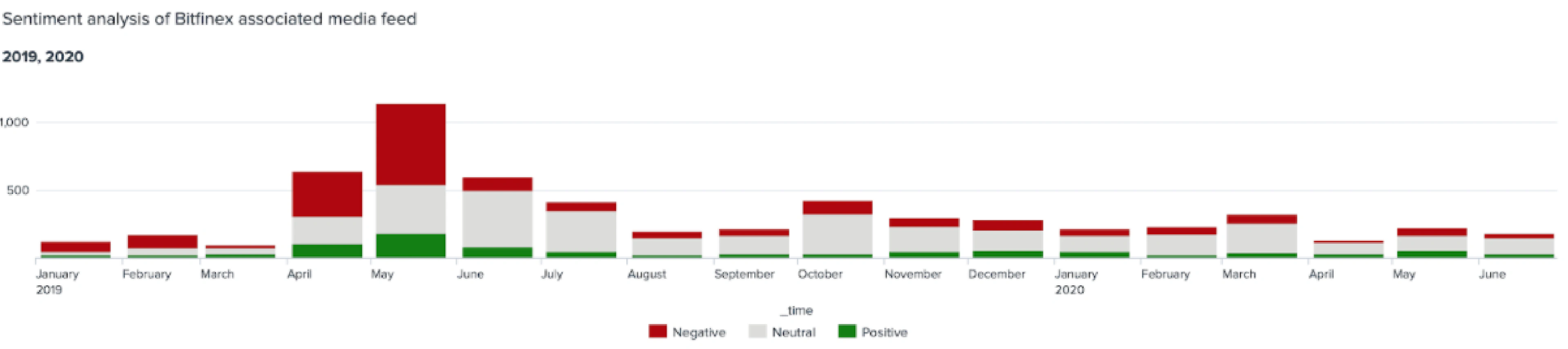

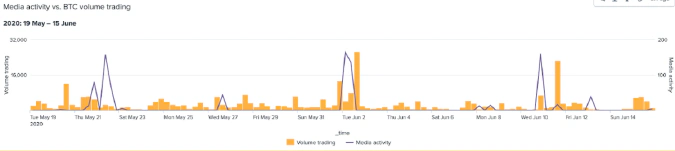
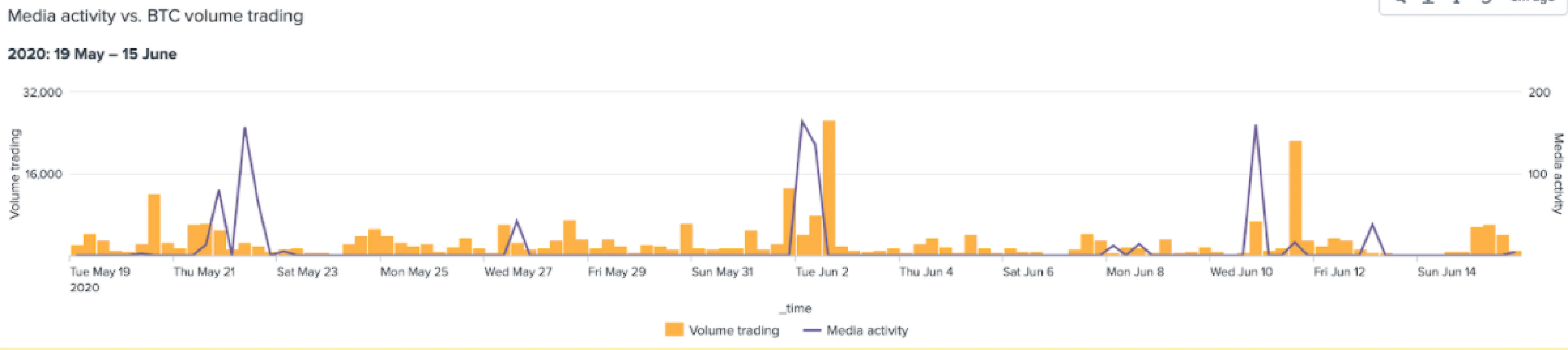
The movement of money occurs in several tranches, which each time causes a rapid news flow, as can be seen in the chart below. Although transactions can be observed online, it is difficult to determine the owners of addresses and wallets. Moreover, attackers are likely to use VPN technology in order to hide the real address of transactions. Attempts to link bitcoin transactions to geolocated IP addresses have little to no use when dealing with sophisticated attackers capable of subverting security measures of Bitfinex and BitGo.
The attractiveness of the cryptocurrency market for the criminals stems from the simplicity of creating the bitcoin address, the lack of verification requirements, and the absence of any limits to the number of addresses that one person can create. It all establishes the conditions for multiple fraudulent activities that are quite difficult to expose.
The second move of the stolen funds was noticed a month later on August 12, 2019. That time hackers moved another 300 BTC, preliminarily splitting it into 10 smaller transactions. Coin mixing platforms appear to be one of the key tools hackers used to stash the stolen funds.

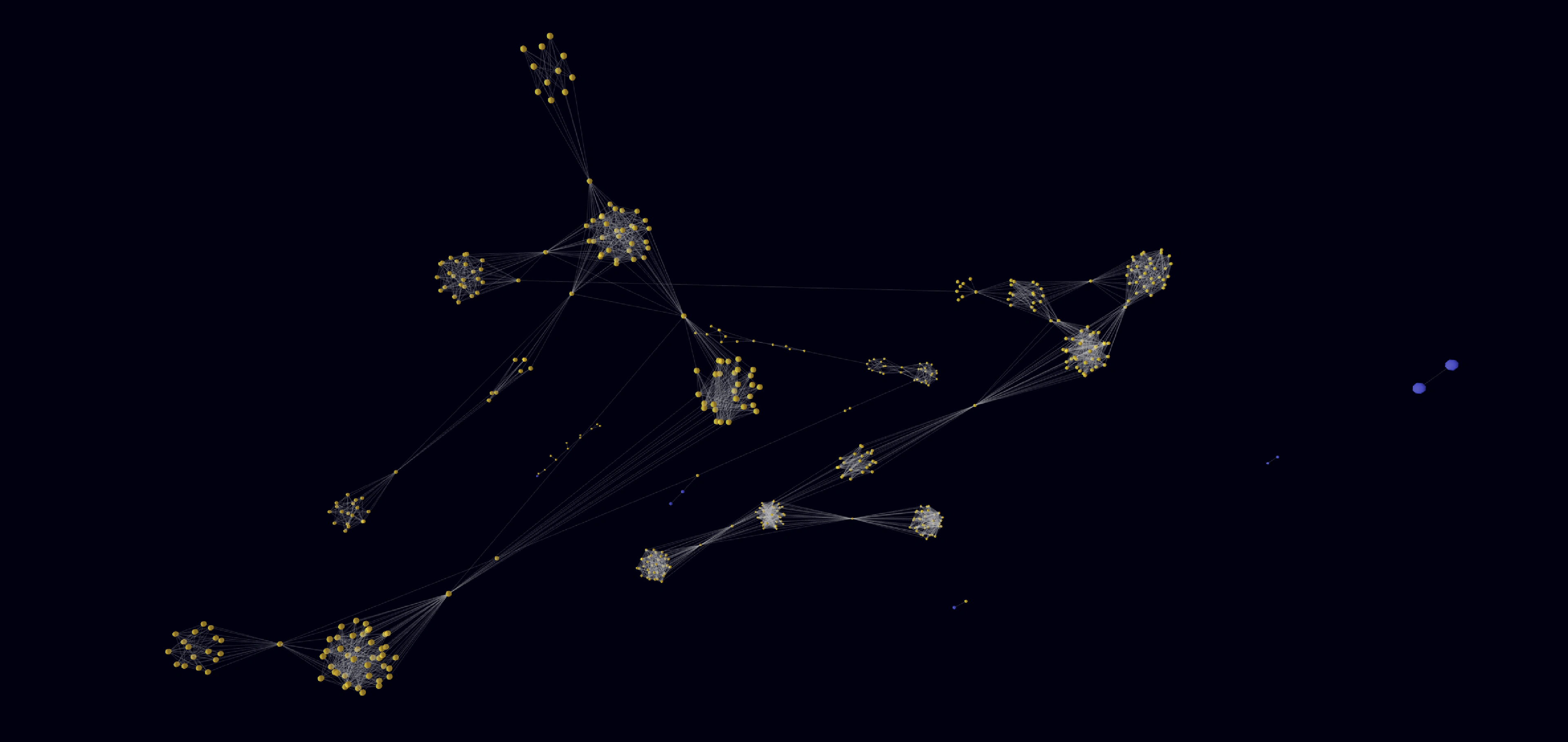
The graph above represents the flow of the stolen bitcoins. It’a 3D model that shows the network of transactions that have been made from the addresses, directly or indirectly connected with the Bitfinex hack. The blue nodes stand for the addresses associated with the Bitfinex hack, whereas yellow ones are the new addresses, through which parts of the stolen funds have moved. Each edge stands for a particular transfer of the stolen funds. The transaction volumes are mostly very small. Otherwise, the alert is triggered.
Only a small number of addresses are undoubtedly associated with the Bitfinex Hack. Most of the addresses that are involved in transactions are new and very likely belong to hackers. Their transaction history is limited to the dates the stolen funds were on the move.
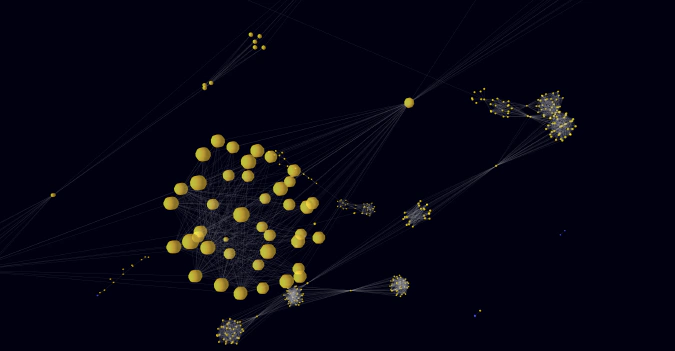
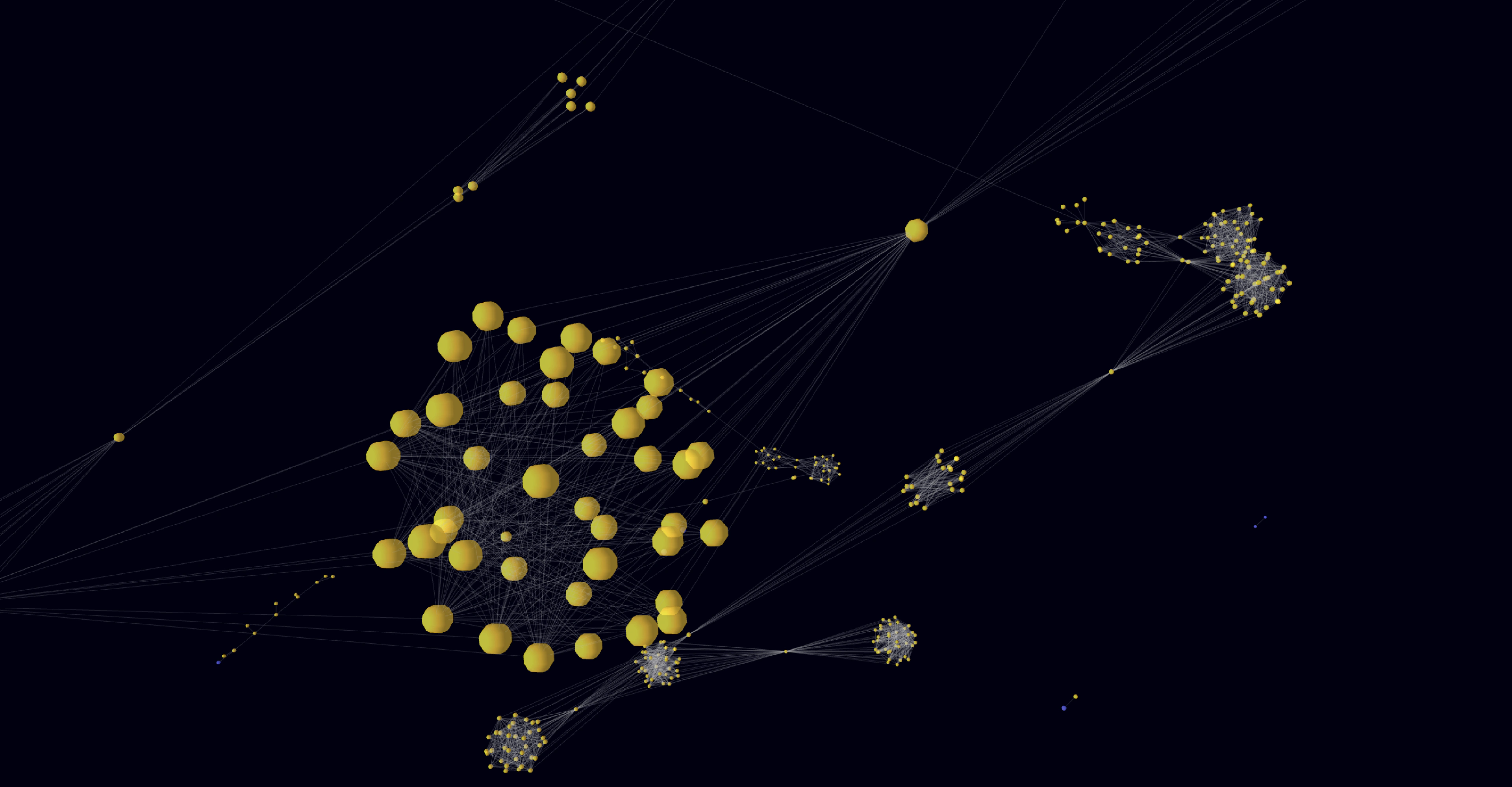
Bitfinex hackers’ scheme seems to incorporate traditional money laundering techniques: in order to avoid detection, they split up the large transaction into tens of smaller ones, which makes it harder for the exchanges, legal authorities, investigators to track the assets. The coin mixing process can be easily observed on the graph above. The big clusters of nodes show how the sources of the coins are masked by a number of intermediate transactions. After being blended in the coin mixer and then paid out to the intended recipients, stolen assets are moved further without anyone knowing it’s “dirty”.
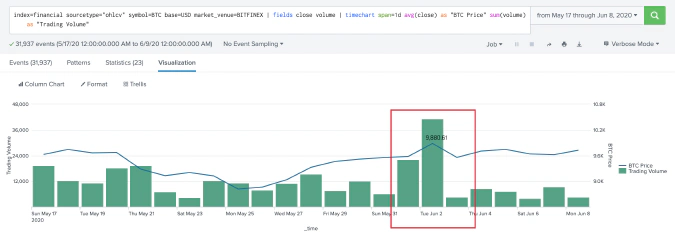
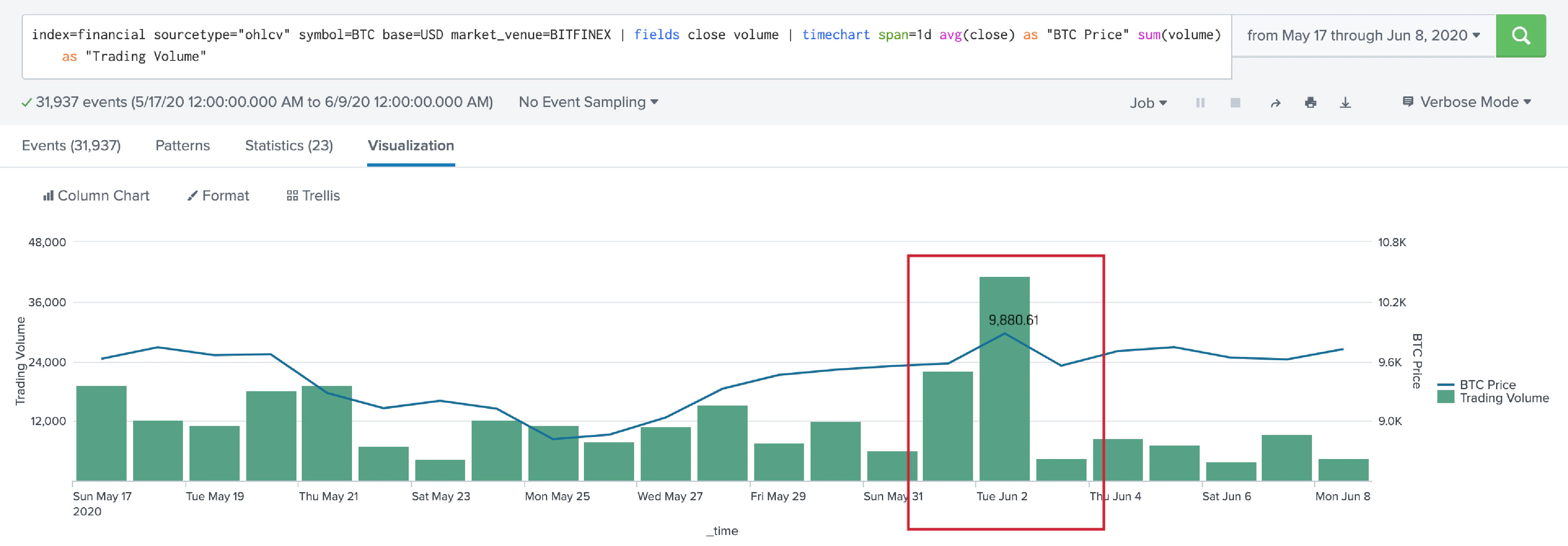
Almost a year after, on May 21, 2020, 30 coins from the August 2019 transaction were transferred again. Not so long after, on June 2, 2020, another move of approximately 80 BTC to an unknown wallet was reported. Finally, the latest move of the stolen assets was observed on June 11, 2020. It was the biggest one as well. Hackers transferred 416 BTC in 20 separate transactions. Having followed their scheme, they made a transaction in accordance with a new BTC price spike: price rocketed up with a further dramatic drop. Based on observations, such price patterns could indicate large currency holders manually keeping price at a certain level in the market. Some traders fear that the hackers might dump the Bitcoin on the market which could result in the Bitcoin price collapsing.
The move of the stolen funds resulted in the increase of the trading volumes as well. Trading volume spikes are observed specifically on laundering money dates from the graphs below. Corresponding significant jumps in trading volumes once again confirm the influence of the size of the hackers’ stash and its potential influence on the whole market conjecture.
Taking into account the analytical findings of this investigation and the details of the original security breach, we are dealing with sophisticated attackers who are familiar with traditional blockchain forensics methods. They transfer the stolen assets in small amounts, constantly obfuscating their trace via coin mixing services. For almost four years that have passed since the hack, no investigation succeeded in either revealing criminals’ identity, or retrieving any meaningful amount of the stolen funds. This confirms that classical blockchain forensics approach proves itself insufficient in this case. Instead of following the long and tangled path from one node to another, we suggest paying more attention to the correlation of different types of data to better understand the broader pattern of crypto custodian attacks and the following money laundering schemes.